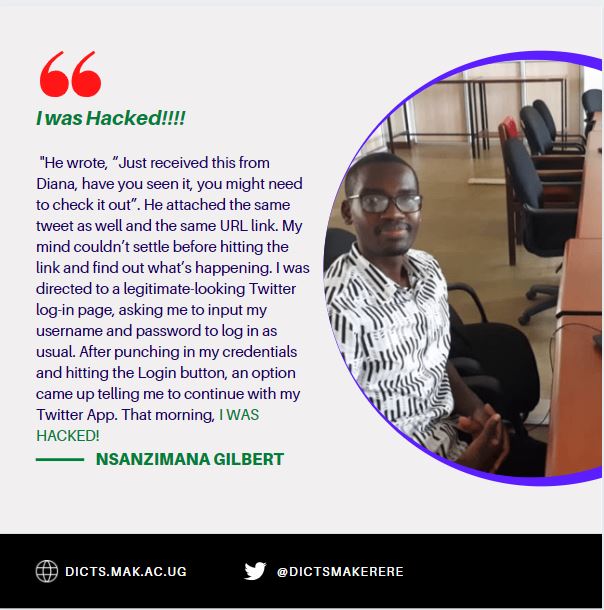
By Nsanzimana Gilbert
My Hacking Experience—Learn from the victim
It was one of those mornings just like the previous ones, I got to my working table and begun by checking out my WhatsApp inbox. One of my teammates sent me a message that my previous tweet had “made news”. “Check out what people are saying about this tweet” was the message with a screenshot of the tweet itself and a URL link to hit and check what people are saying. Bad or good? I am now about to become a star? Before I could even open up to check, another teammate (our supervisor) also sent me a WhatsApp message telling me the same. He wrote, “Just received this from Diana, have you seen it, you might need to check it out”. He attached the same tweet as well and the same URL link. My mind couldn’t settle before hitting the link and find out what’s happening. I was directed to a legitimate-looking Twitter log-in page, asking me to input my username and password to log in as usual. After punching in my credentials and hitting the Login button, an option came up telling me to continue with my Twitter App. That morning, I WAS HACKED!
Social Engineering
Social engineering is the type of Phishing that happened to me and I was the victim. Through social engineering, the attacker makes sure that you are enticed by the message and after you are prompted to click a link. In order to achieve this, sometimes they employ people close to you who may either know what’s happening or be innocent as well.
Phishing is a type of cyber-attack that is mainly intended to steal your personal sensitive data such as credit card numbers, social media account credentials, organizational account credentials, or even installing malware on your computer.
How You Finally Get Hacked
After clicking the link, a legitimate-looking but Fake page opens up and to the unsuspicious person, it really looks legitimate. As you punch in the login credentials, they are actually captured and received by the hackers. The hacker impersonates an organization that you trust and that’s how you feel untroubled to submit your details. Your account is now in their ownership and they can use it to their benefit.
The prominent entry through which the social engineering hackers launch their attacks is via email. It makes up 96% of all the social attacks according to the Data Breach Report2020.
Social media influencers are also moving targets for phishing attacks. One of the incidents is for a young lady, 24-year-old from Californian Lindsie Comerford. Criminals posed as a brand interested in sponsoring her. They inquired “What is the cost of an advertising cost on your Instagram page”. The received email included a convincing-looking link that appeared to go to the real sender’s (Criminals in this case) Instagram account. Instead, the victim was directed to a fake Instagram login page, as she logged in, the victim’s password was sent to the hackers. That day, her email, online banking, and Instagram account which had more than 41,000 followers were all taken.
Takeaway
- Observe URL links keenly and think before visiting them.
- Be sure to verify the sender’s address before clicking any link. It can look legitimate but with a slightly small variation
- If suspicious, don’t go on. Give yourself time to think about it.
- Use the official websites or mobile apps in case you are being prompted to check your updates.
