By Arthur Moses Opio
Key Points
- Email remains the number one attack vector.
- 90% of Phishing happens via email
- Backing up data must be practiced at all times
Ransomware is a big problem that keeps presenting itself. Until someone has been hacked, you can not know the importance of cybersecurity awareness, end point solutions, and general human behavior as users surf the web.
The Number One Attack Vector
Email remains the number one attack vector that is used by hackers to spread malicious software.
Due to our continued awareness of Cybersecurity, we continue to get feedback and incident reports from you. Thank you for your vigilance thus far.
Unfortunately, sometimes these malicious emails can bypass. Our security filters on webmail have been reconfigured and we keep monitoring daily, but we can't monitor how one behaves with their email accounts while subscribing to websites, newsletters, etc. We cannot know the safety of some of those sites except by telling you to ensure it is https:// and has a padlock sign on it.
Backup At All Times
Recently, one of our users was attacked by ransomware. All the files on the computer were encrypted and they were being asked to pay money. paying money does not guarantee that you will get your files back and also paying the ransom fuels and facilitates the dark trade over the internet. Imagine all your research work, reports, and MOUS encrypted., that can be devastating.
We want to encourage you to always back up, do not say that you cannot be hit by ransomware or any other kind of virus or spam ware.
Do Not Click Any Link Or Download Any Attachment
From the analysis, we have done. The attachments that the user got were word files that end with the extension details.txt and envie.eml. The message that came from this email shows that the user email<benitosara@portugalmail.pt> was unknown and rejected by our system but it returned with two attachments that have been listed above. We have already blocked the email.
Always read before you click, think before you download or click. Get us to scrutinize and get back to you with more information.
Change Your Password, Get Your Computer Scanned
When you see such things, please report the incident. If you have accidentally clicked, change your password to your emails and also seek for your computer to be worked upon by your college system administrator.
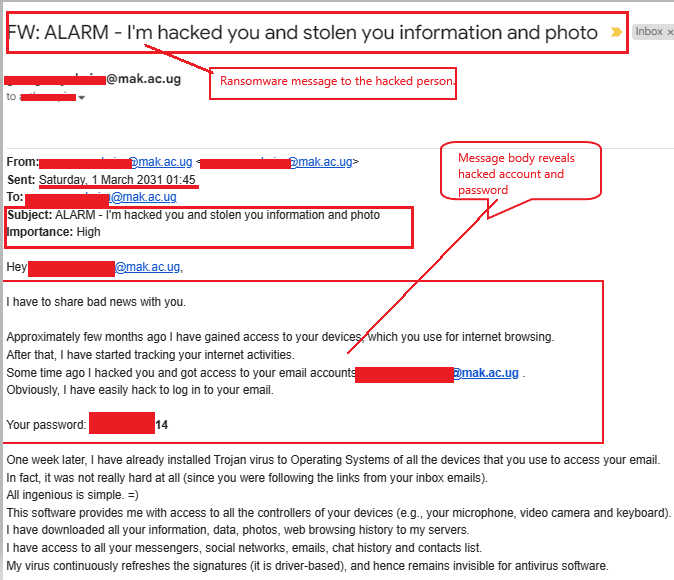
One of the emails received, the user got a message saying,
First of all, the Subject had Typos, and this is how it looked like.
ALARM - I'm hacked you and stolen you information and photo, then the body of the message was
"I have to share bad new with you, Approximately few months ago I have gained access to your devices, which you use for internet browsing. After that, I have started tracking your internet activities. Some time ago I hacked you and got access to your email accounts abc.bcd@mak.ac.ug .Obviously, I have easily hack to log in to your email. Your password: xxee@2022 "
Clearly that message alone will reveal your email and password and that's already a sign that you have been hacked.
The same body of the message has a bitcoin link and the hacker said,
"Here is my bitcoin wallet: bc1qrtjncfxsju56l0px5tmupf56l7q7asut03a929"Then it has a lit of Do nots, Do not reply, try to contact police, find me, etc.
And further says, things you don't need to worry about:
*That I won't be able to receive your funds transfer.
- Don't worry, I will see it right away, once you complete the transfer, since I continuously track all your activities (my trojan virus has got a remote-control feature, something like TeamViewer). etc.Then lastly, the hacker says,
"One more thing... Don't get caught in similar kind of situations anymore in future!
My advice - keep changing all your passwords on a frequent basis"
Indeed, we should always change our passwords, a recommended practice is every 3 months. This is because passwords and emails are often breached through such attacks.
Always go to https://sso.mak.ac.ug to change your password whenever you feel something strange is happening with your account and most importantly back up, you can use one drive, google drive, and off-site backups like USB disks, etc.
Get Us The Email Header
When you are reporting the incident, beyond the email you will be forwarded to us. There is what is called the EMAIL HEADER, it has more details like IP addresses that we can get to block as well.
This video link guides you on how you can get us the header.
Be safe online, we are better off safe than sorry.
Be Cyber Smart
For any ICT inquiries, do not hesitate to reach out to us.
Regards
