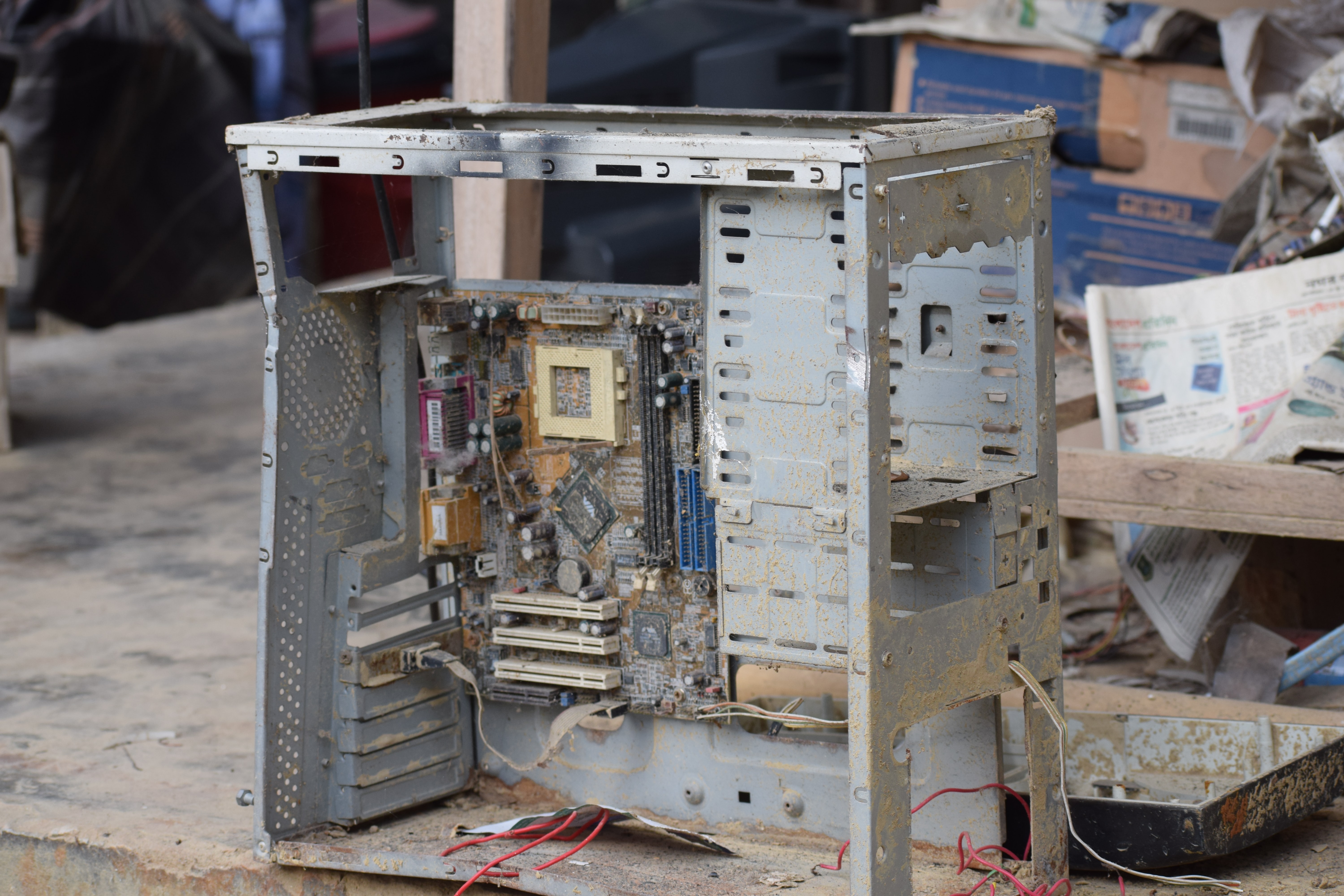
Do you have an old computer? if you do, you might need to ask yourself if it is really safe to continue running on old technology.
As the old saying goes, you can not put new wine in an old wineskin, if you do it will burst. Old computers or devices can not run new software, this is basically because the new software is not built for the old technology. It is like forcing a big foot into a small shoe, the outcome is that the shoe will give way.
In the ICT space, many people tend to avoid upgrading in the name of saving costs, but they don't know that it could be more costly running old technology in the long run.
ICT Trends Towards The End of The Year
We are entering a season where promotions will be on the high. You will get links and attachments in your inbox telling you about discounts on items you have liked. Remember to have your cyber antennas alert because, with the free gifts, there could be a hidden agenda by some cyber actors. Some will pretend to be all sorts of people and their plans are to dupe you so that they can still from you. So be careful about unsolicited links or attachments that will come to your inbox. Don't just click, tame your appetite to click.
Keep Your Guard Up
Now that many works from home, cybercriminals have found many ways to dupe them. A lot of things happen in the work environment(physical work and telecommuting) and in cyberspace. Promotions are created by cyber actors to gift people smartphones or anything that appeals to their eyes. These links with these products come compromised and with just a click, a download or installation of the malware can happen on your computer or smartphone.
Workers are normally tired and end up forgetting to do basic computing practices like updating their computers, logging out of applications, or even locking their computers.
Let us look at the example of logging out of applications. If a survey was done right now, many of us would be found not to log out of everyday working applications like email. The excuse we normally give is that we just want to open the browser and log in quickly without having to input a password. We are better off being safe than sorry.
Leaving such applications like email, social media accounts open makes it easy for an attacker to do whatever they want because they will already find your gadgets with access to critical services that are pertinent to work and your personal life. Cybercriminals are not sleeping, they are very awake and as you perform keystrokes on your computer, a trojan malware could be recording everything you do.
We do encourage staff and students to keep their guard up and to make sure that even as the year ends, your cyber antennas are active(up and running) not down and dysfunctional.
Obsolete Devices
Using obsolete devices is a global trend and a global problem. Many enterprises or institutes have their reasons for not changing technology or even upgrading software. Not doing so has far-reaching risks than can be very devastating to institutional and personal assets(data).
These are some of the risks associated with running obsolete devices;
1. The product will no longer receive security updates from its developers, increasing the likelihood that exploitable vulnerabilities will become known by attackers.
2. The latest security mitigations are not present in older products, increasing the impact of vulnerabilities, making exploitation more likely to succeed, and detection of any exploitation more difficult.
This is what we are up to when we run obsolete products
A business falls victim to a ransomware attack every 13.275 seconds (Cyber Defense Magazine).
43% of cyber attacks target small businesses and only 14% are prepared to defend themselves (Small Business Trends).
3. Lack of flexibility - Old technology can not perform like new technology. This disadvantage limits anyone'ss business’s flexibility in various areas including data analysis, which helps businesses, organizations, institutions make better decisions moving forward, as well as communication and collaboration with the team.
4. Decreased Productivity - If you have ever seen rainbow lines across your screen, this is a clear sign the computer is old. An individual working on a critical report on such a computer could take up to 30 minutes waiting for the line to clear, this decreases productivity, lost productivity could lead to lost revenue.
Do you have hundreds of files all over your computer storage with no clear organization? This makes it more difficult to search for the exact files you need. Without proper search and organization programs, you’ll lose an unnecessary amount of valuable work time. Updated technology makes it easier for employees to store and locate information as well as streamline their workflow.
How To Manage Risks From Obsolete Products
With many constraints running from policies, funds, etc. What can only be done without old technology is to manage the risks hence reducing the impact.
1. Reduce the likelihood of compromise by preventing the devices from accessing untrusted content (effectively making it hard for malicious content to reach the device and exploit it)
2. Reduce the impact of compromise by preventing access to sensitive data or services from vulnerable devices (so even if the devices are compromised, the damage will be minimized) We should implement a combination of these two approaches. In the long-term, moving away from obsolete systems should be the goal.
If you have an obsolete computer, device, this is critical information.
Source (National Cyber Security Center)
